Effectively use limited resources. Eliminate the most cyber risk in your organization.
Organizations that use the risk-based vulnerability management method will suffer 80% fewer breaches.
*Gartner, “A Guide to Choosing a Vulnerability Assessment Solution,” April 2019
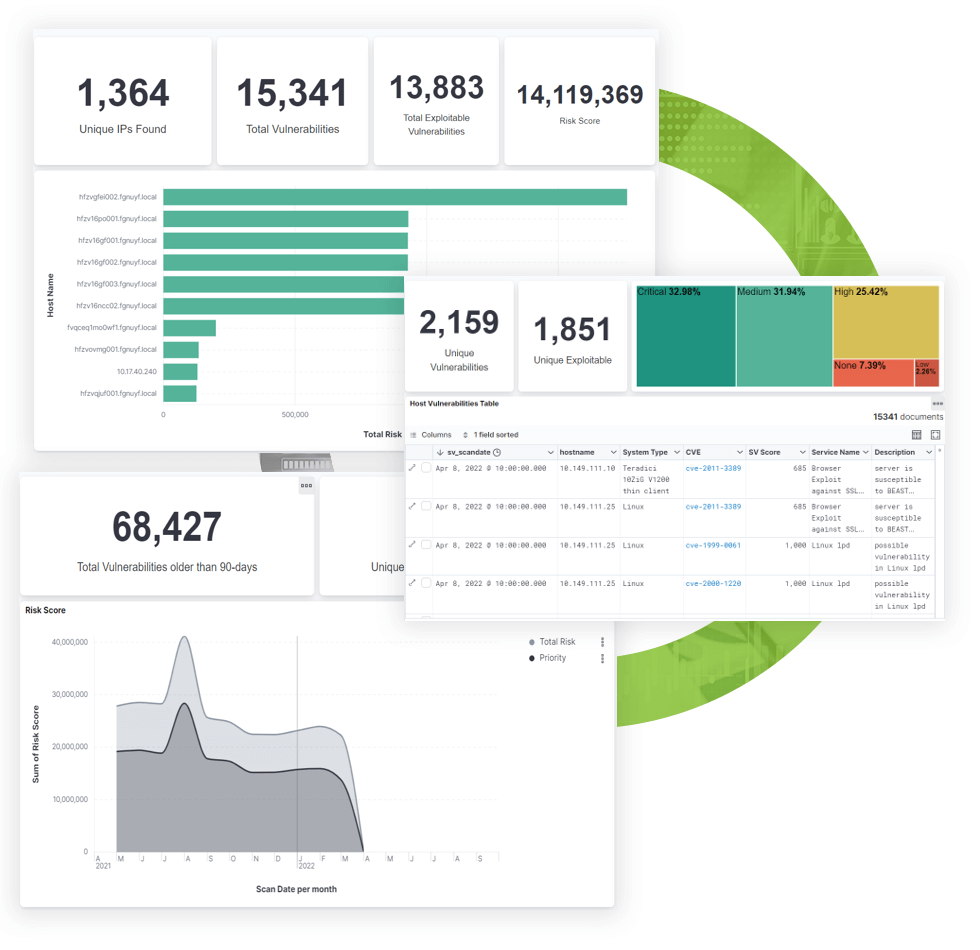
Leverage predictive prioritization to deliver true risk-based vulnerability management with TARA.